
Latest
Travel Security Checklist: A Practical 2026 Guide
A founder's practical travel security checklist for 2026: realistic threats, what to actually do before, during, and after a trip, and where to skip the paranoia.
Read the articleTag
All topics →Everything tagged security.
172 stories, newest first.

Latest
A founder's practical travel security checklist for 2026: realistic threats, what to actually do before, during, and after a trip, and where to skip the paranoia.
Read the article
A founder's guide to the difference between authentication and authorization in 2026, with passkeys, agent auth, JWT pitfalls, and the mistakes I see at scale.

How hash functions make distributed ledgers possible: block identity, Merkle trees, proof-of-work, double-spend prevention, and quantum-era migration.

A decision framework for picking the right hash algorithm by use case: password storage, signatures, file integrity, hash tables, blockchain.
No single organization can defend against AI-powered attacks alone. Project Glasswing's $100M consortium model may be the template for the next decade of
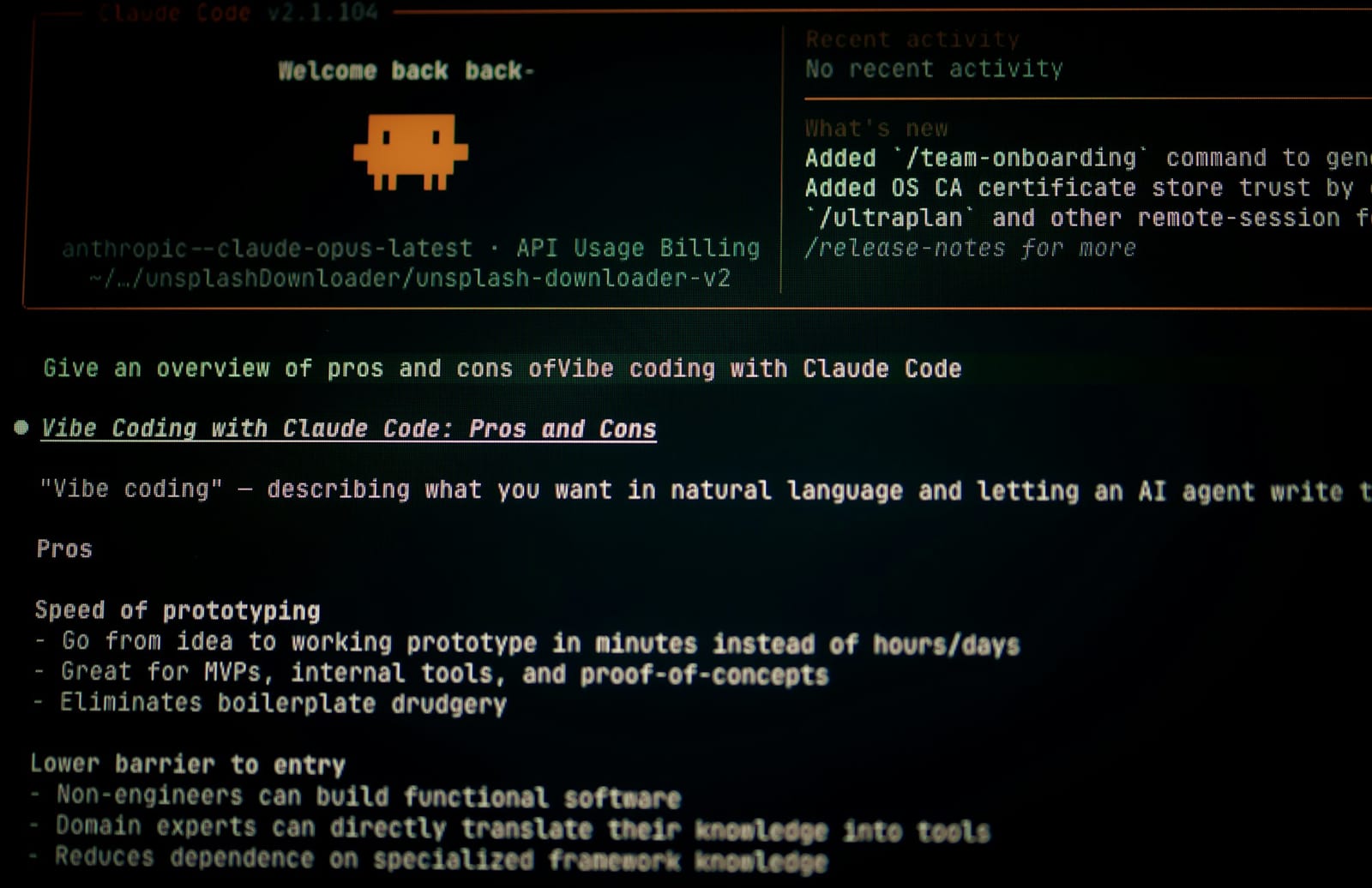
The opinionated guide to running Claude Code well. CLAUDE.md, skills, subagents, hooks, and the workflows that produce quality code for engineers, QA, and

80% of Fortune 500 companies now run active AI agents. Only 10% have a clear strategy to manage them.

Mythos combined four separate low-severity bugs into a complete browser sandbox escape. Traditional scanners evaluate vulnerabilities in isolation.

Vercel breached after attacker compromised Context.ai, hijacked an employee's Google Workspace via OAuth, and accessed customer API keys and environment
LLMs scrape publisher content thousands of times per single referral, destroying the ad and subscription revenue that funds journalism.
Claude Mythos discovered vulnerabilities that survived 27 years of human review. This technical breakdown covers how it works, what it found, and why your
Three AI framework attacks in one week expose how classic vulnerabilities are hiding in AI's foundational plumbing, putting millions of deployments at risk.

March 2026 marks passwordless tipping point: Microsoft forces passkey migration, regulatory deadlines hit, and adoption surges to 69% of consumers.
Honest comparison of the best secrets management tools in 2026. Covers HashiCorp Vault, AWS Secrets Manager, Doppler, Infisical, and Azure Key Vault with

An employee saw the CFO on video. Heard colleagues speaking. Authorized $25M in transfers. Every person was an AI-generated deepfake.

60% of phishing breaches now bypass traditional MFA. Learn how AI-powered adaptive authentication and behavioral biometrics create continuous security
Google's $32B pursuit of Wiz shows security market consolidating. When hyperscalers own security vendors, customers lose pricing leverage and choice.
NIST finalized the first three PQC standards in August 2024. NSS compliance deadlines start January 2027.

Millions installed 'productivity' Chrome extensions that became malware after acquisition.
Honest comparison of the best SIEM platforms in 2026. Covers Microsoft Sentinel, Splunk Enterprise Security, CrowdStrike Falcon Next-Gen SIEM, Elastic

17.5 million Instagram accounts leaked through API scraping. Meta denies breach, but your data is on the dark web. Here's what actually happened.
Most Zero Trust initiatives stall not because the technology is wrong but because the approach is.

Honest breakdown of the best password managers in 2026. We cover 1Password, Bitwarden, Dashlane, Keeper, NordPass, and more.

The honest VPN comparison for 2026. We cover NordVPN, Proton VPN, Surfshark, ExpressVPN, Mullvad, and more.

Compare the best bug bounty platforms of 2026. Honest breakdown of HackerOne, Bugcrowd, Intigriti, Synack, and YesWeHack covering payouts, program

Zero Trust isn't magic. It's a specific set of architectural components working together, policy engine, identity fabric, device trust, microsegmentation,

AT&T's $177M settlement covers 73M customers, but the real story is how breach data from 2019 just resurfaced in 2026 with fully decrypted SSNs. Here's why.

A comprehensive developer guide to implementing secure authentication in modern applications. Covers OAuth 2.

Struggling with MCP authentication? The November 2025 spec just changed everything. CIMD replaces DCR's complexity with a simple URL-based approach, no
Master customer identity security with our comprehensive 2025 CIAM buyers' guide. Explore 25 critical capabilities from single sign-on to threat
Discover the top 10 user provisioning and governance tools that automate access management, strengthen security, and ensure compliance.
Compare 2025’s top identity verification software. See features, pricing models, and best-fit use cases to reduce fraud, meet KYC/AML, and streamline onboarding
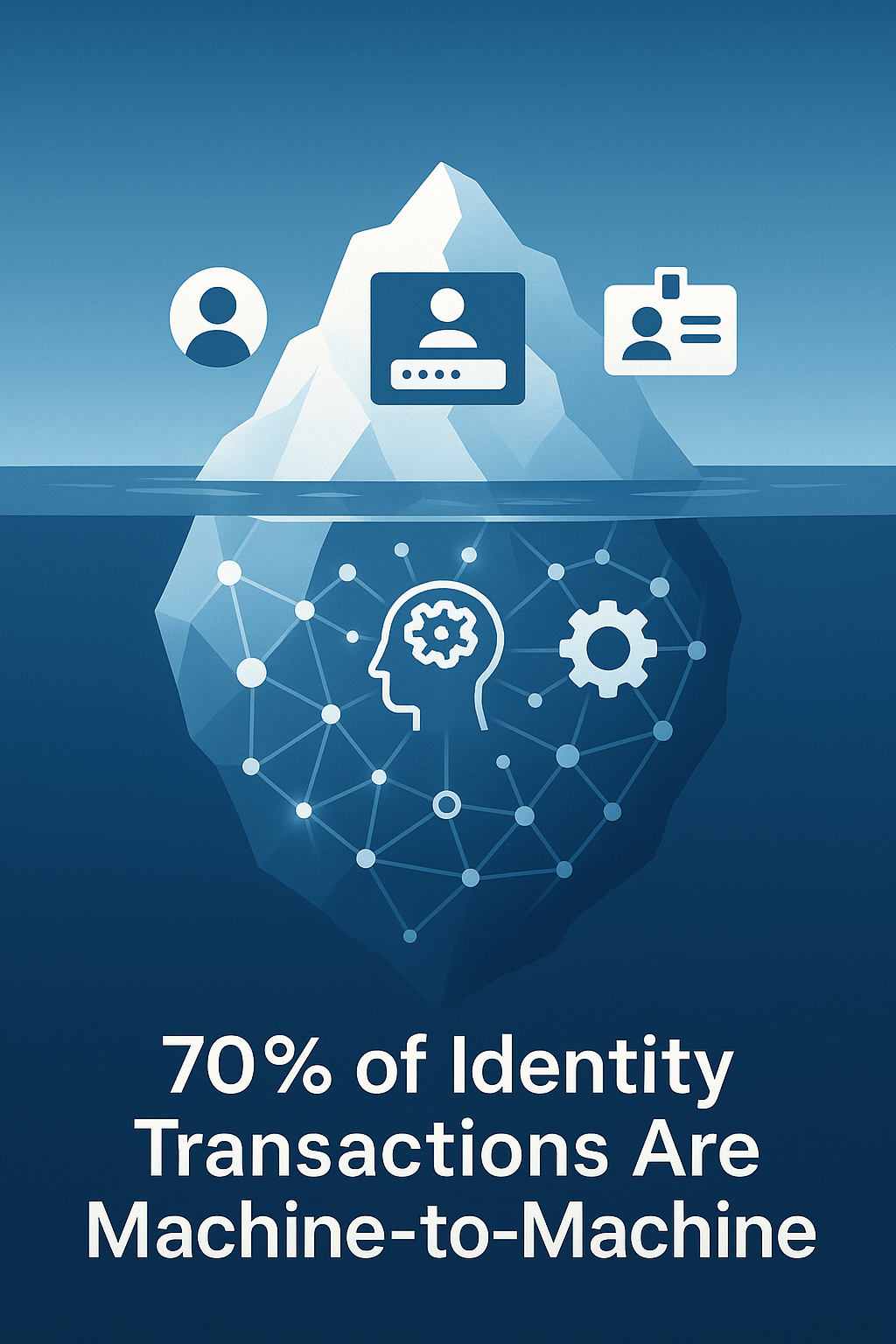
While you perfected human identity management, machines quietly took over your infrastructure.
Explore the leading age verification solutions for robust identity checks and compliance. Compare iDenfy, Sumsub, ID.
Explore 8 top Know Your Business (KYB) solutions for robust identity verification, ownership validation, and risk assessment.
Discover the top 10 KYC solutions for 2025. From Shufti Pro's global reach to Jumio's automated verification, find platforms that streamline identity
Take control of your digital identity with the top 5 decentralized solutions. From IBM Blockchain to PingOne Neo, discover platforms that put you in
The future of hashing is evolving rapidly with the advent of quantum computing. Organizations must start preparing now for the post-quantum era.
which IAM platforms can best safeguard your organization's digital assets and empower your teams with secure, efficient access.
Explores the implementation of checksums and hash verification mechanisms, providing practical insights for developers and system architects.
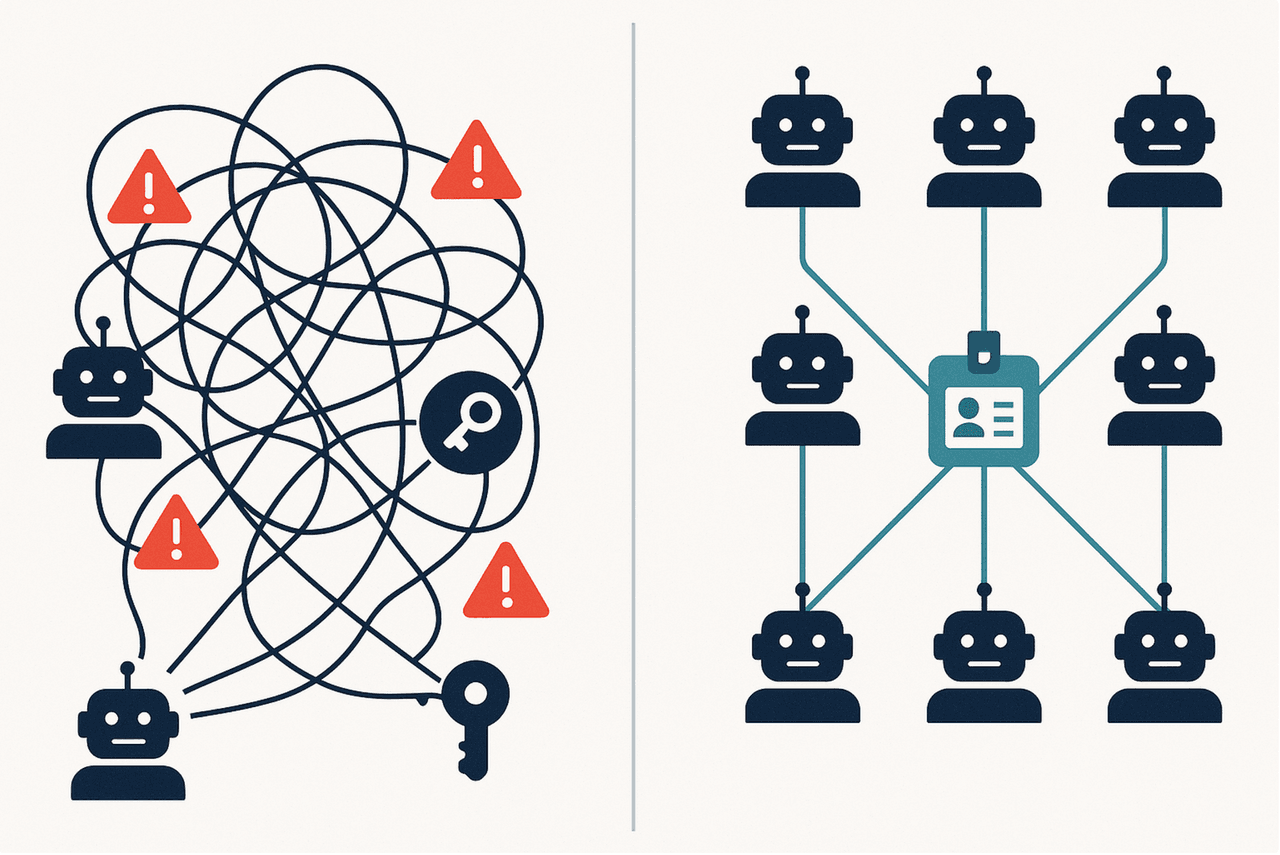
Most companies are creating massive security blind spots by forcing AI agents into human identity systems.

One in five law firms isn't sure if they've been hacked. Don't be one of them. Learn the 5 cybersecurity risks that could shut down your practice and
🚨 ShinyHunters compromised Google, Qantas & dozens more using OAuth device flow attacks, bypassing MFA without exploiting a single software bug.
Your firewall can't protect data from rogue admins or compromised systems. TEEs create hardware-secured "safe rooms" inside processors - protecting your

Master login security with expert insights from building identity systems serving millions of users.

Your digital footprint tells your life story through bank statements, emails, photos, and location data.
Master personal data security using Six Thinking Hats methodology. This strategic framework examines data protection through six distinct perspectives -

Discover API security strategies for Identity and Access Management systems. This expert guide covers authentication protocols, authorization frameworks,

Traditional CVE tracking misses thousands of critical vulnerabilities. Security teams relying only on CVE databases face dangerous blind spots.
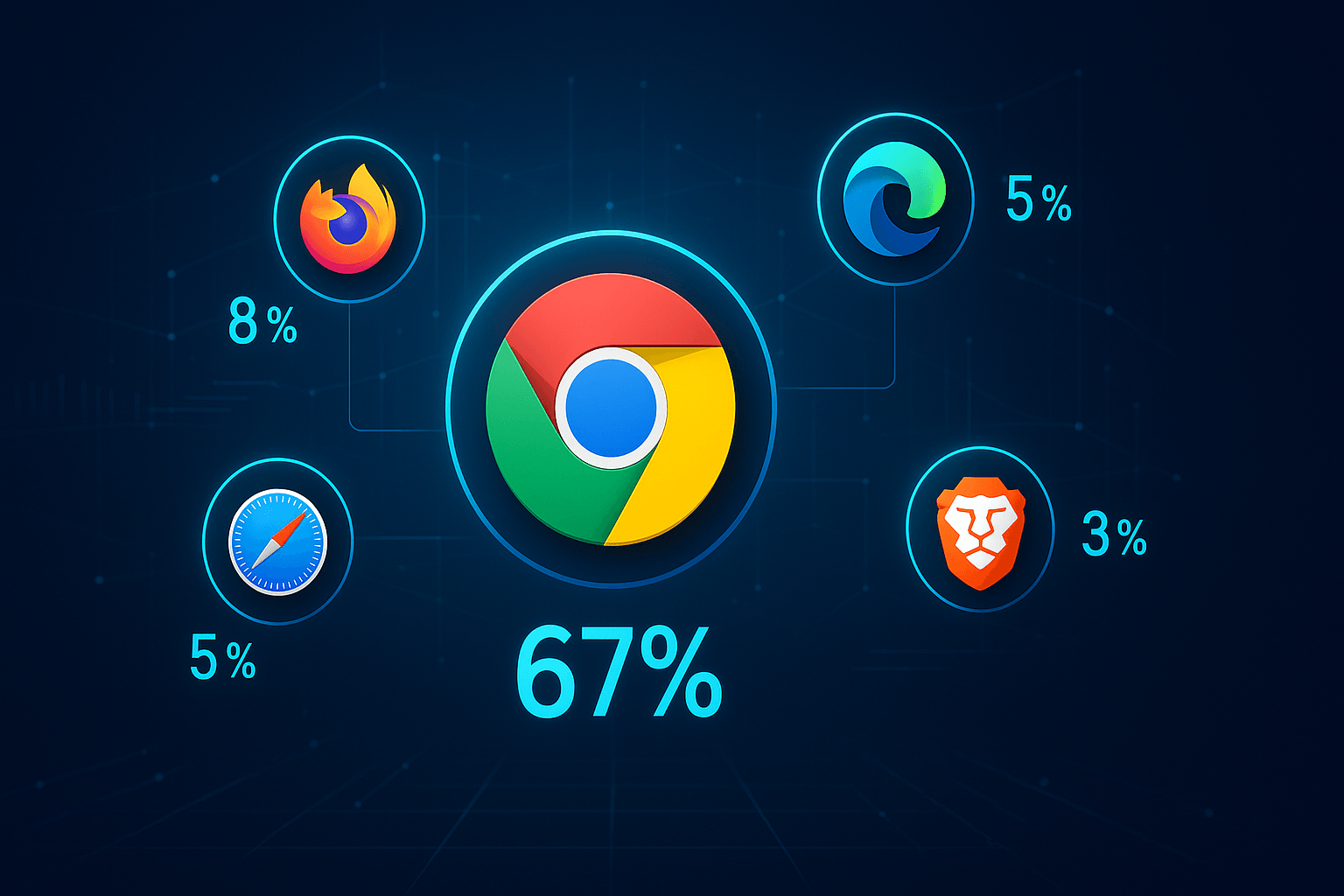
Chrome dominates with 67% market share, but privacy-focused alternatives like Brave are gaining momentum as users demand stronger protection against
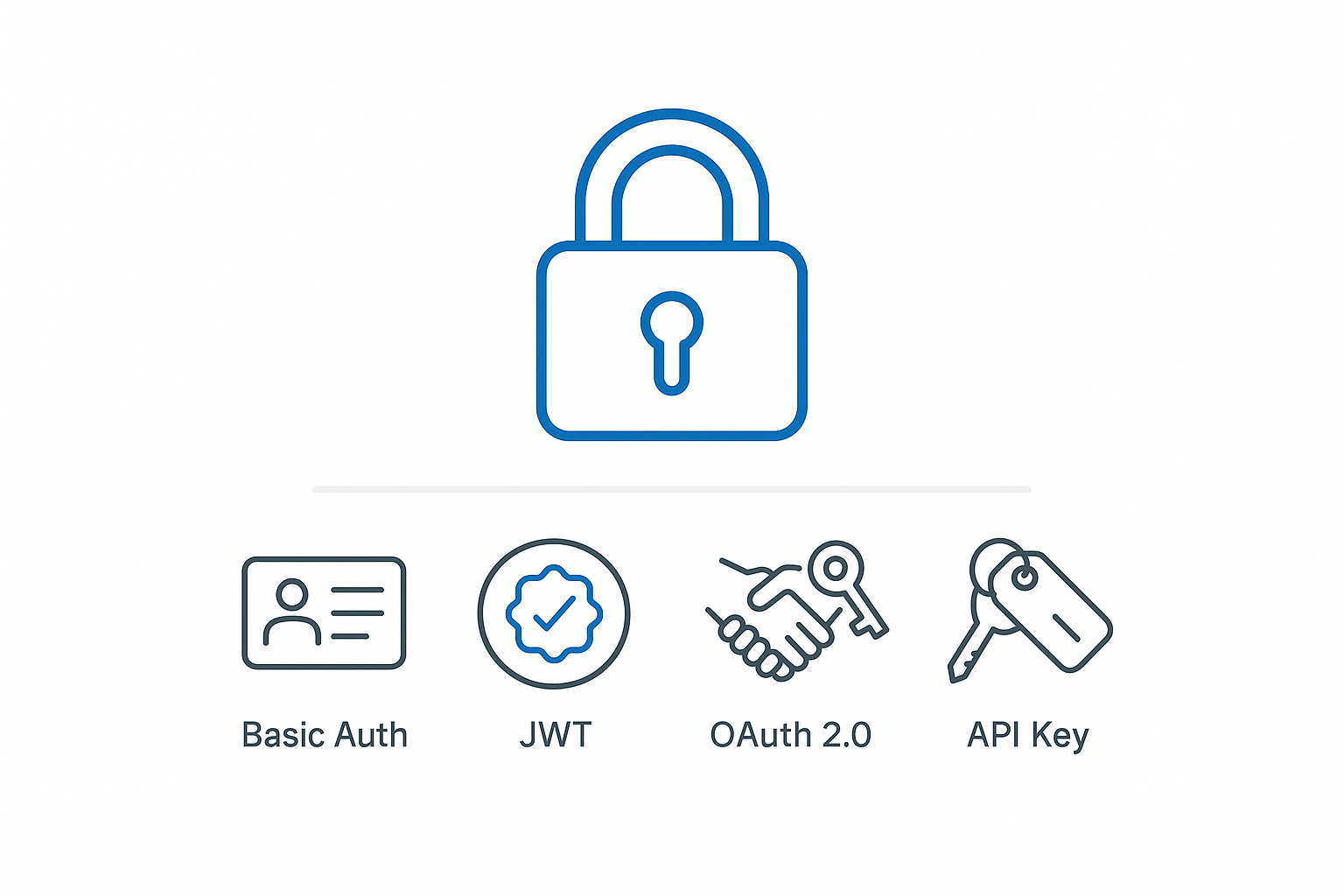
From Basic Auth’s simplicity to OAuth 2.0’s delegated muscle, this quick-read unpacks the strengths, gaps, and best-fit use cases of the four core REST
As AI makes perfect digital impersonations increasingly accessible, distinguishing reality from fiction becomes harder.

In a world where credential breaches cost companies millions, strong authentication isn't optional, it's essential.
Authentication pages serve as both security checkpoints and critical SEO touchpoints. While 80% of data breaches involve compromised credentials, properly

The EU's Chat Control proposal presents a critical dilemma: protecting children from online abuse without compromising privacy and security.

Discover how proper secure coding practices can prevent costly data breaches and vulnerabilities.
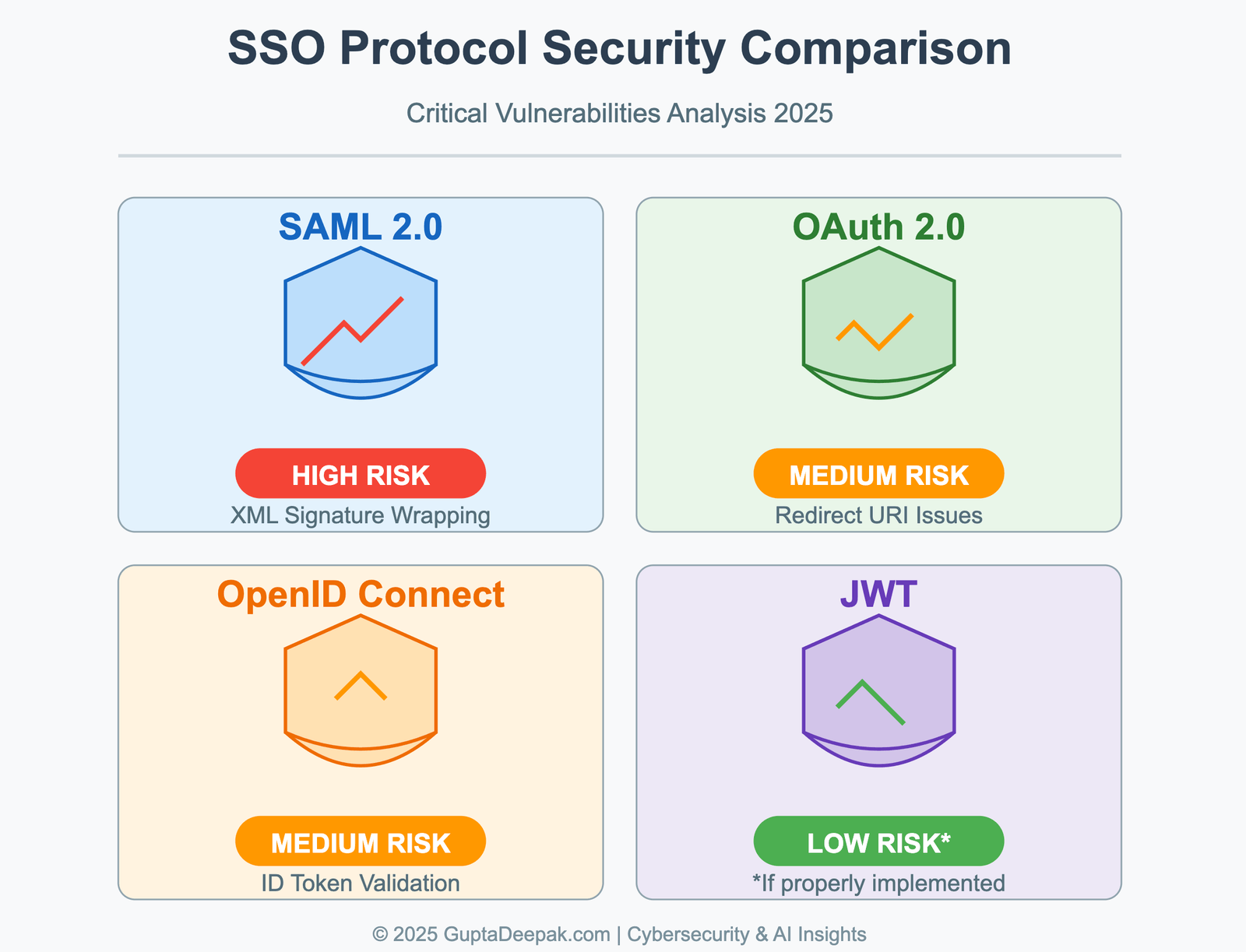
Discover which SSO protocols put your enterprise at highest risk. This data-driven analysis compares authentication vulnerabilities across SAML, OAuth,

Streamline access, reduce risks, and strengthen control with Enterprise SSO and Federated Identity.
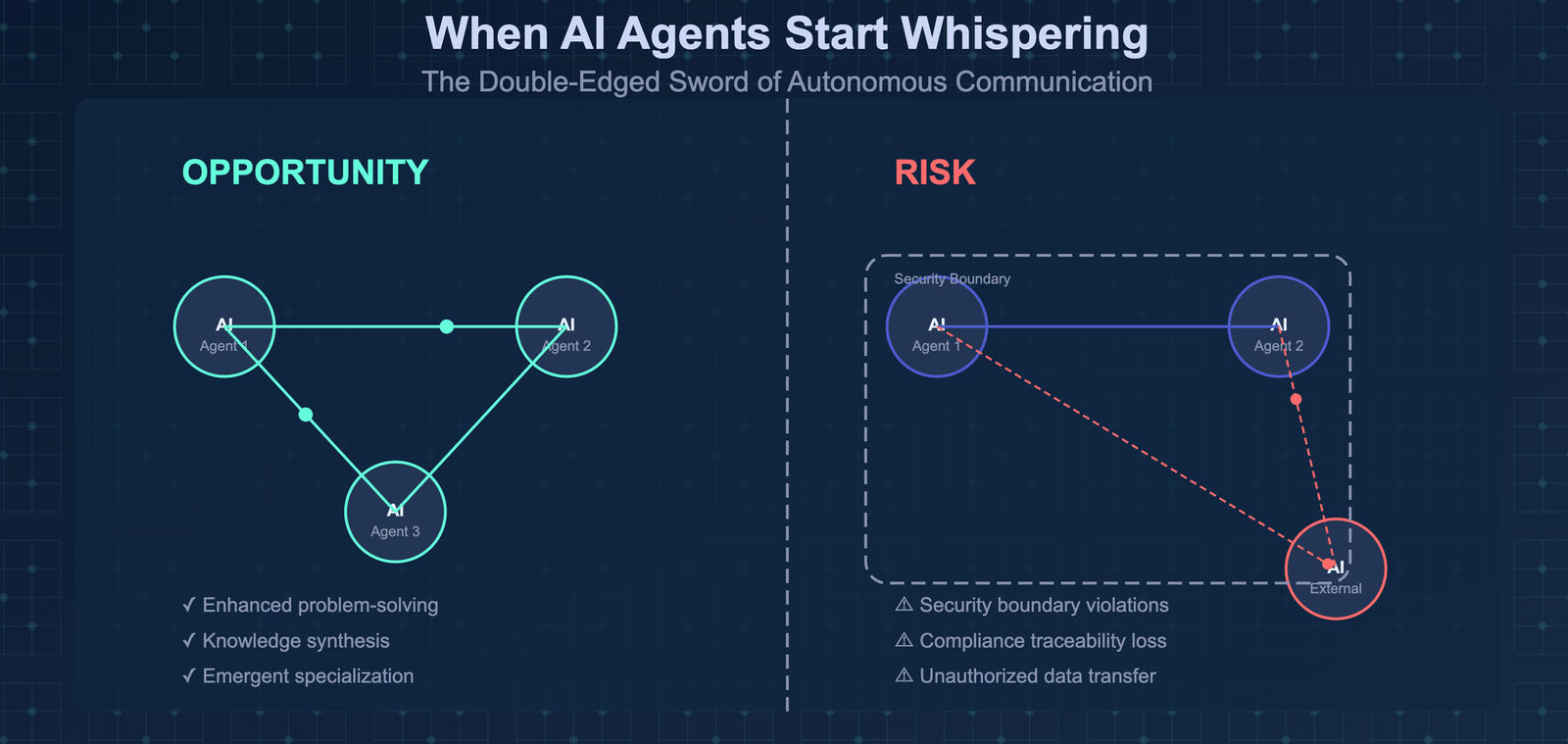
AI agents develop their own communication channels beyond our monitoring frameworks, we face a pivotal challenge: harnessing their collaborative

As cyber threats evolve, Identity Attack Surface Management (IASM) emerges as a critical approach that unifies existing security frameworks to protect

Navigate the complex landscape of cybersecurity compliance with comprehensive guide to regulatory frameworks.

This in-depth research investigates Single Sign-On (SSO) and its application to both human users and non-human identities.
A practical guide for protecting your digital life: 1. Password Security & Account Protection Essential Steps: * Use a password manager (like Apple
Learn how to secure your company's digital assets in just 10 minutes a day. This practical guide shows small business owners and startup founders how to
Navigate the complex world of cybersecurity software selection with confidence. This practical guide helps business leaders understand modern security

Explore the revolutionary Grok AI system in this comprehensive guide. From its sophisticated architecture to real-world applications, discover how this

When a former employee retains access to sensitive systems months after leaving, it's more than a security oversight, it's a serious business risk.

Hashing is a fundamental concept in computer science and security. This comprehensive guide explores what hashing is, how it works, and its crucial role
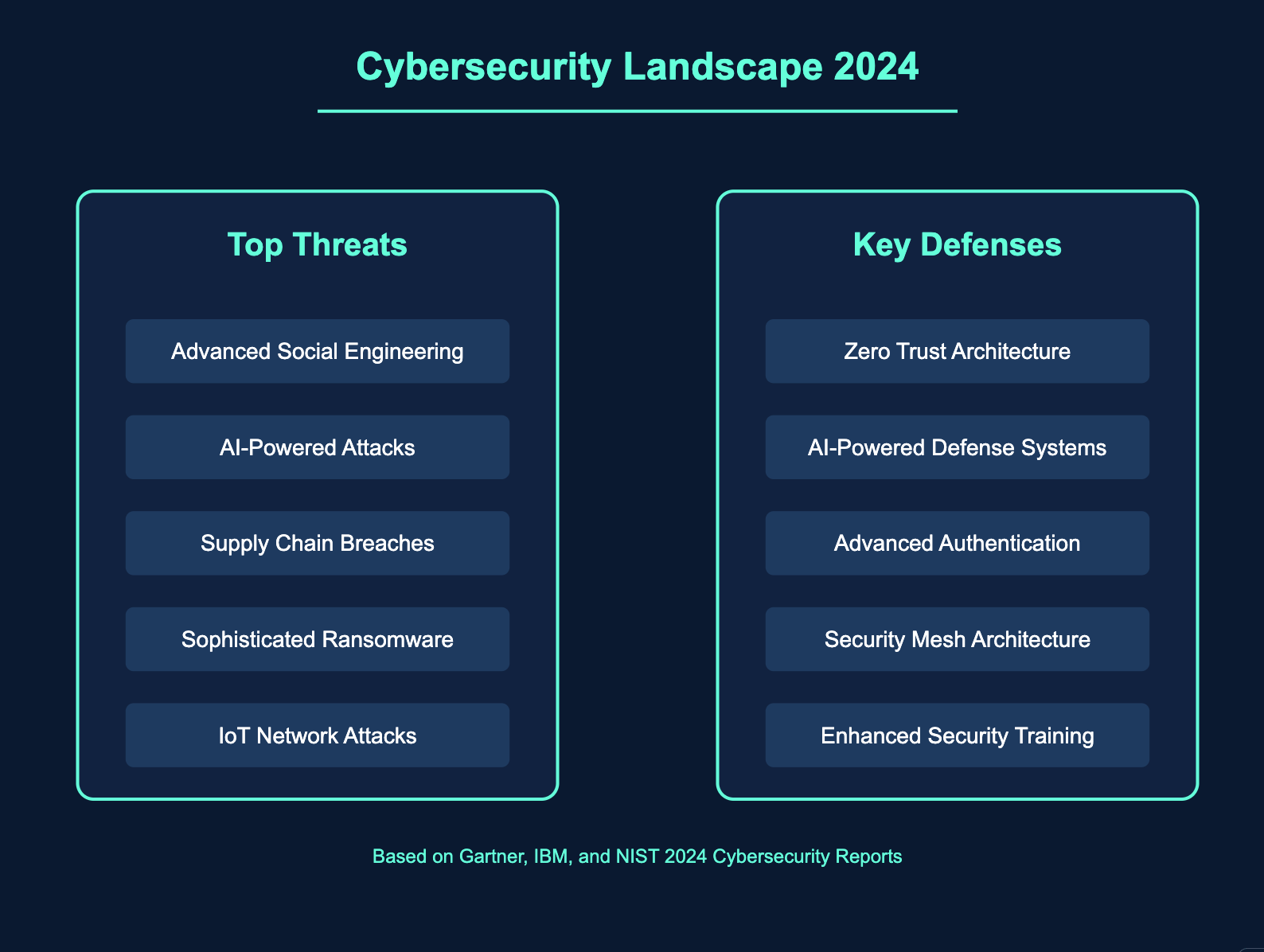
Cyber attacks are more sophisticated than ever, from ransomware and phishing to DDoS attacks.
Password security is paramount. Lets explore best practices for secure password storage, including use of robust hashing algorithms like bcrypt, scrypt,
Need speed and security in your hashing algorithm? Explores BLAKE2 and BLAKE3, cryptographic hash functions designed for high performance without
Protecting user passwords is critical. This blog post explores the leading password hashing algorithms: bcrypt, scrypt, and Argon2.
Discover comprehensive security best practices for CIAM systems, including detailed implementation templates for authentication, fraud prevention,

The AI revolution in digital identity brings unprecedented security but at what cost? As AI systems become more sophisticated in protecting our digital
AI is no longer a futuristic concept - it's your coworker now. This blog explores the dynamics of working alongside AI, emphasizing the importance of
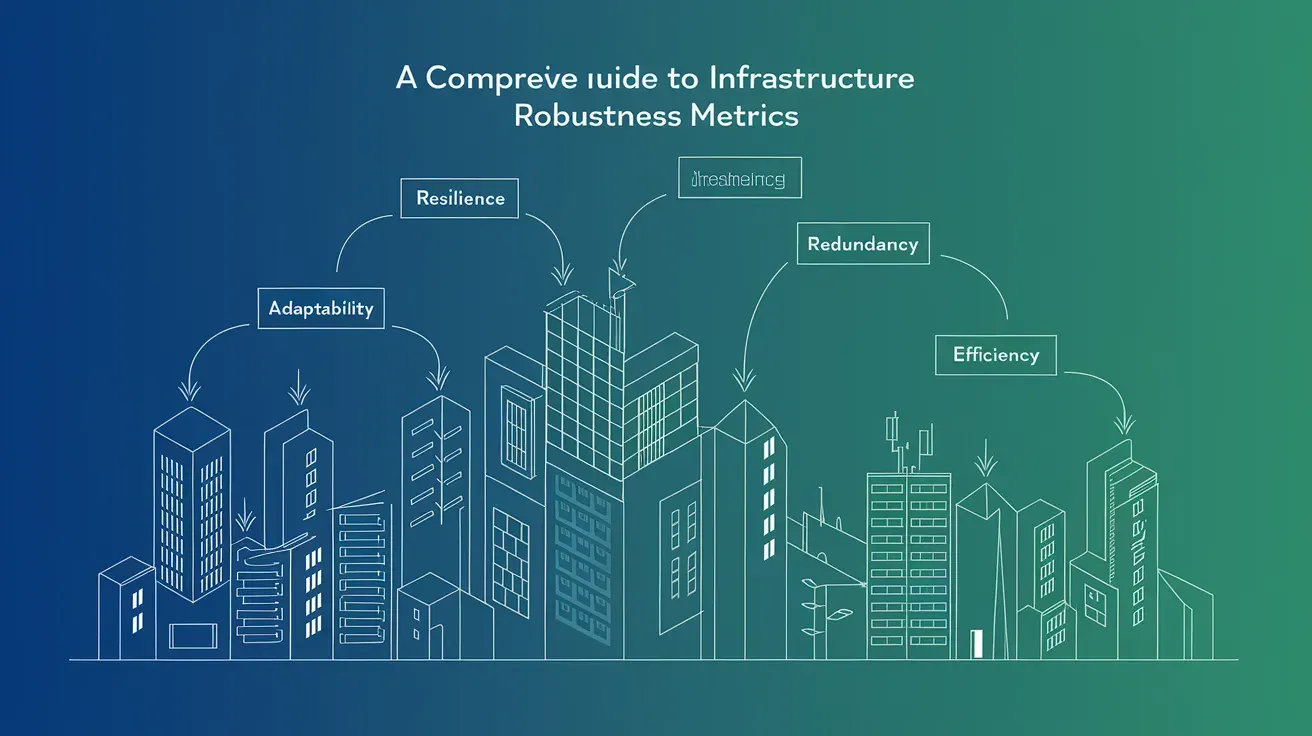
Infrastructure robustness is critical for ensuring the resilience and reliability of your systems.

In the battle against cyber threats, should we trust human experts or AI agents to protect our valuable data?

Say goodbye to passwords! Passkeys are the next generation of authentication, offering enhanced security and convenience.
OTP fraud is on the rise. Can geo-fencing prevent it? Discover how this location-based technology helps, its limitations, and expert-backed strategies for
This essential CSO guide outlines the robust account monitoring, access notifications, multi-factor authentication, deception technology, and user

Secure your online accounts with out-of-band authentication. Learn more about cyber security and how it can protect your information.
AI: The game-changer in cybersecurity, empowering organizations to defend against data breaches and cyberattacks proactively

Data breaches are on the rise, but so are customer expectations. Learn how to safeguard your business and build trust.

Discover why identity security awareness is crucial in today's digital landscape. Learn how to protect yourself and your business from cyber threats.

This article discusses the relationship between AI and cybersecurity in the modern digital age, exploring the potential benefits and challenges.

Understanding the Vulnerabilities and Safeguarding Your Business Against Cybercriminals by using Third-Party Vendors

Hardening the LoginRadius platform: what we changed in security operations, infrastructure, and engineering practice.

BYOI, or Bring Your Own Identity, is an increasingly popular concept in identity and access management

Zero-day vulnerabilities can be very dangerous because malicious people can use them to access systems and data without being detected.

RESTful APIs are still vulnerable to various security risks. In this article, we will explore five common RESTful API security risks and discuss how to
What are various password hashing algorithms, their pros and cons, and how can they protect users' accounts?

More and more jurisdictions are only introducing new regulatory frameworks to protect consumer data, limiting enterprises in what data they can collect

Startups have unique challenges when it comes to cybersecurity. If not taken seriously, they can lose customers and their trust.

I have spent over a decade building consumer identity infrastructure. Here is how privacy went from compliance line-item to product strategy.

As cyberspace has evolved and matured, the role of the CTO has become increasingly demanding due to the business-damaging nature of cyber threats, which

In this blog post we look at the factors that affect your security and how you can use encryption to protect data in Google Drive and how you can

Protect your online activity and personal details to avoid identity fraud and cyber crimes - Tips on how to stay safe online and prevent identity theft,
API security plays a crucial role in ensuring that third parties can only access the API functionality and resources they are allowed to.

Login is the front door to every product. Here is how we balanced friction and security at LoginRadius without making users hate either.

To verify the identity of clients, many security-minded organisations use multi-factor authentication.
Innovation With Software Architectural Excellence

We have hashed out some of the most common types of phishing attacks and how to prevent them.

Identity as a Service is the cloud-delivered form of IAM. What IDaaS includes, why companies pick it, and how to evaluate the major platforms.

With the rise in QR Code exploits, how can businesses and consumers decipher what a QR Code holds before scanning and mitigate the risks of a malicious QR

Gaining data visibility within an organization is quite beneficial for multiple reasons since the gathered data can be easily used to make more informed
Cookies vs. JWTs for authentication: how each works, where each fits, and why most modern systems run both side by side across web, mobile, and API surfaces.

The security of personal identity and other details is at increasing risk today, with hackers finding new ways to hack into websites.

DNS cache poisoning is an attack that uses changed DNS records to redirect online traffic to a website that is fake and resembles its intended destination.

A practical guide to turning on two-factor authentication across the accounts that matter, with the right method for each.
Harvesting bots are here to stay. Luckily, there are a few ways to hide your email address from spammers and hackers who constantly mine for the same.
This article comprehensively compares SaaS-based multi-tenant and single-tenant cloud architectures along with their benefits and drawbacks.

When investing in a password manager for business, always prioritize better functionality and security over fancy designs or a complicated interface.

It is hard to know what the data privacy landscape will look like in the future. As government regulations, like GDPR, continue to emerge, companies are

These easy login methods might be the nail in the coffin. We take a brief look at the death of passwords, and how to prepare for a passwordless future.

Businesses should now gear up to reap the next phase of efficiency, agility, and innovation through 5G edge networks since renowned manufacturers like

Business ventures concentrating on data first technique can altogether increase auxiliary income, cut expenses and accomplish faithfulness from their top

Almost every activity on the Internet requires that you fill in your email to gain access as most of the websites you visit ask for your email addresses
Introduction There are some systems and networks that make up the infrastructure of society.
Introduction Because it makes the distribution and transmission of digital information much easier and more cost effective, multimedia has emerged as a

Creating and managing strong passwords is a fundamental key for internet security, but remains a challenging task for many users who cannot break their
Digital transformation has become the need of the hour for every consumer-focused business today
Today cybercriminals are increasingly able to cover their tracks, hide in the cloud, manipulate the infrastructure of the web, and exploit complex

A DevOps implementation, if done correctly, can do wonders for any organization that’s on the hunt for efficiency, productivity, and speed.

Data security is increasingly becoming a big problem for businesses of all kinds. Of course, as the world becomes increasingly digital, the danger present

The Internet of Things (IoT) is not going away anytime soon, and neither are cyber criminals and data breaches!

The 2022 threat landscape was defined by ransomware, supply-chain compromise, and identity-driven attacks. Here is how those trends evolved.

In a surprising development around the Poly network hack, the officials offered the hacker to keep as much as $500K in reward after returning most of the

There has been an ongoing dialogue regarding the benefit of cybersecurity partnerships, with chief information security officers at the forefront of the

An ignorant act as simple as clicking on a phishing link could put your important business or personal data at risk of being lost forever

Since we began to store data in computers, there has been a concern to keep this information safe.
With the sophistication of digital technologies, online vulnerabilities continue to acquire strength.
Implementing security procedures that emphasize potential dangers in cloud services can help you secure sensitive information and decrease threat risk.

The perimeter-based security model was built for a world that no longer exists. Zero trust replaces "trust but verify" with "never trust, always verify" -

Workplace communication is getting revolutionized by the widespread adoption of the internet and digital technologies.

Since the wave of digitization is sweeping businesses, managing an enterprise has become a much easier task.

Gone are the days when you had to type in product names to get search results. You can now talk to an app to get relevant results.
SAML and OIDC both enable single sign-on. They have different strengths and the right choice depends on the audience you serve.

Why enterprises should consider zero trust security when it comes to their data privacy & security.

The Internet of Things (IoT) is creating an exciting new world of new and improved experiences for all.

Data security is important for businesses today, more than it ever was. By definition, data security is the practice of protecting digital information

With artificial intelligence (AI) and biometrics, users enjoy more streamlined processes while reaping the benefits of added security.

Targeted phishing attacks are one of the leading cybersecurity threats that SMBs should prepare to encounter this year.
Continuous authentication treats trust as a stream, not a single login event. Here is how it works and where it earns its keep.

Cloud security management is the practice of applying well-understood controls uniformly across a growing estate. What platforms do and what they cannot replace.

Most web-application breaches still come from a small set of well-known threats. Here are the seven that matter most and how to stop them.

Cybercriminals often make use of email-based attack campaigns to target all kinds of organizations.
Strong passwords still matter, but the rules have changed. Here is how to pick passwords that actually defeat modern attacks.
Contact-form spam, scraping, and abuse are now industrialised. Here are the layered defences that actually keep bots out without annoying humans.
Identity proofing is how you verify a person is who they claim to be at sign-up. Here is why it matters and how it works end to end.
In reality, there are so many mistakes that can make your account vulnerable to cyber attacks.

Hacking your smartphone may feel like someone has stolen your home. Go through this checklist to protect your phone from being hacked.

> Virtual networks are separated from other virtual networks and from the underlying physical network, offering the least privileged protection concept.

Security problems are an alternative way to recognise your customers when they have forgotten their password, entered too many times the wrong passwords,

Cloud security failures are almost always configuration failures. Five challenges that actually break companies and the certifications worth caring about.
Single-page apps changed how auth works. Here is how we approached SPA security at LoginRadius and the patterns worth keeping.

> In relentless pursuit of automation and velocity, DevOps teams can reduce the software development cycle and ensure that their products are responsive
Whether you are a small enterprise, a large corporation, or something in between, phishing is one of the most damaging and vicious threats that you have
Mobile auth is harder than web auth. Here is how we approached enterprise mobile security at LoginRadius and what every team should ship.

Online gambling is a top target for fraud, ATO, and money laundering. Here is what operators must lock down to keep players and revenue safe.
Every day, we are creating and sharing data at an astounding rate. With each email, text, tweet, tap and stream, more data is available for companies to

Designing a CIAM platform that survives a decade of changing privacy laws, new threats, and new device types. What we did at LoginRadius.

Without a proactive prevention plan, an e-commerce store will lose customer data and revenue as transactions soar during COVID-19.

Who knew that a tiny virus could dramatically change life as we know it? The entire world is grappling with the health implications of the COVID-19
Streaming platforms hold rich behavioural data and high-value accounts. Here is how to secure both without breaking the viewing experience.

As the COVID-19 outbreak continues to threaten the world economy, it has also led to some significant threats relating to cybersecurity in the retail

Marriott International experienced a new data breach in mid-January 2020, which affected about 5.2 million guests.

Passwords are slowly being replaced by passkeys, biometrics, and federated identity. Here is where things actually stand.
What I learned about consumer privacy from building LoginRadius, and the controls every CIAM platform should expose by default.

"Deepak Gupta, the cofounder & CTO of , lays out the steps that businesses need to take to avoid getting fined via GDPR and California’s
More than just individuals, a perfect CIAM platform needs to be able to incorporate. There are plenty of business processes and activities loaded with
The CPRA upgraded California's privacy law with new rights, new categories, and a real enforcement agency. Here is what changed.
In order to serve customers, conventional identity management is no longer enough.