Demystifying JWT, OAuth, OIDC, and SAML: A Technical Guide
Dive into a clear technical guide explaining JWT, OAuth, OIDC, and SAML. Learn their strengths and weaknesses and use cases to choose the right approach for your next project. Stay updated with 2024 best practices and unlock seamless user experiences!
Applications and APIs today need to handle user authentication, authorized access controls, and identity management, leading to the common question - which standard is right for a given use case? Core standards include JSON Web Tokens (JWT), OAuth 2.0, OpenID Connect (OIDC), and SAML, each with distinct approaches. This comprehensive technical guide explores the key characteristics, appropriate integration scenarios, and relationship between these pivotal protocols for securing systems and data in the modern enterprise.
JSON Web Token (JWT)
Overview
JSON Web Tokens represent claims between parties as a compact JSON object encoded into a digitally signed or encrypted bearer credential passed in HTTP requests. JWT encodes assertions like user identity, access permissions and custom attributes.
Structure
A JWT comprises three logical sections:
- Header - specifies token type and algorithm like HMAC or RSA
- Payload - contains verifiable claims as JSON key/value pairs
- Signature - created by encrypting header and payload together
Once the token is generated after initial authentication, applications pass JWTs to enable user access across domains and security contexts, avoiding repeat logins.
Use Cases
Typical JWT applications include:
- Authorization – Validate user privileges and permissions
- Information Exchange – Share verified user data between processes
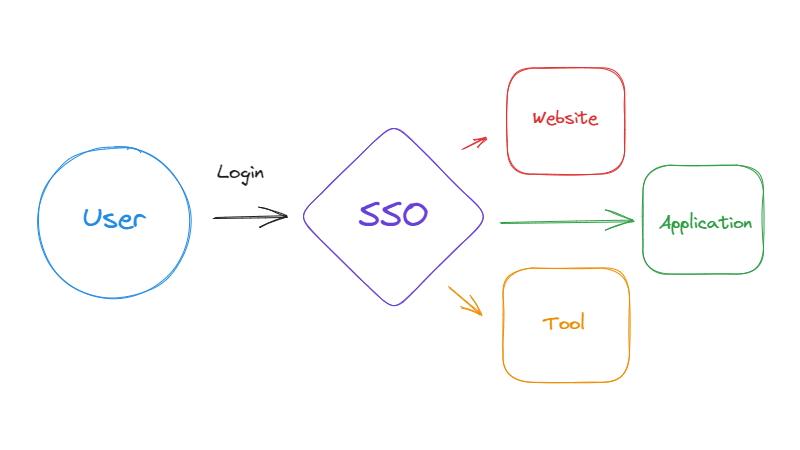
- Single Sign On – Log a user into disparate systems without reauthenticating
Considerations
- Not for sensitive data or long-term use since tokens are often short-lived
- Payloads not encrypted by default
- Revocation support requires token blacklisting, unlike expirations
OAuth 2.0
Overview
OAuth serves as an authorization framework enabling limited third-party access to web resources without exposing user credentials themselves. It provides API access delegation.
Flow Types
OAuth defines several participant roles and standardized flows including:
- Authorization Code - grants code allowing access tokens to apps
- Implicit - directly returns access tokens to clients
- Resource Owner - supplies credentials to client to obtain access
- Client Credential - verifies app identity and permissions to get tokens
OAuth use cases
- Social login with Facebook, Google accessing user data
- APIs allows third-party applications access to functionality and resources
- Financial tech aggregation services accessing bank transaction data
Considerations
- Focus on authorization not authentication
- Bearer tokens allow access to anyone possessing them
- Managing token expiration and revocation remains critical
- Limited built-in user identity handling
OpenID Connect (OIDC)
Overview
As an authentication layer built atop OAuth 2.0, OpenID Connect enables single sign-on and identity exchange capabilities centered around a standards-based user ID token encapsulating verified user identity claims.
an
OIDC overlays enhanced identity handling into regular OAuth flows:
- Authorizing party asks for an ID token
- OAuth server issues signed JWT ID token attesting to authenticated user identity
- Client validates token signatures to establish user SSO session
Use Cases
- Single sign-on portals
- Replacing proprietary federated identity management
- Multi-domain identity layer for web/mobile
Considerations
- Requires identity token parsing and verification
- Logout and federation intricacies exist across domains
- Increased client-side coding even using libraries
- Token encryption remains optional
SAML
Overview
SAML or Security Assertion Markup Language offers XML-encoded schemas for exchanging authentication and authorization credentials between identity providers and service providers.
Roles
SAML involves three roles:
- Principal - the user
- Identity Provider (IdP) - authenticates principal and issues SAML assertions
- Service Provider (SP) - relies on SAML tokens to allow access
Use Cases
Common SAML applications include:
- Enterprise single sign-on (SSO)
- Web browser SSO session portability
- Federating partner identity
Considerations
- XML parsing requires greater processing than JSON-based alternatives
- Features eventual consistency between providers
- Logout coordination intricacies between participating sites
- WebRedirect bindings can raise vulnerability risks
Comparing Architectures and Models
While nuanced differences exist between standards, reviewing deployment models, integration complexity, and broader capabilities reveals core commonalities and distinctions for informing adoption choices:
Decentralized Identity Management
OIDC and OAuth 2.0 adopt user-centric identity models that distribute and delegate access rights across domains via interoperable JSON Web Token credentials. This contrasts with centralized SAML models relying more on pre-integration between identity and service providers beforehand.
Ease of Integration
OAuth 2.0 does not directly specify end-user authentication, avoiding this integration complexity. OpenID Connect essentially layers identity handling atop OAuth access delegation. But SAML federates sign-on directly with relatively heavier initial setup between providers.
Mobile and Device Scenarios
Native and mobile apps gravitate toward baked-in platform support for OAuth authorization flows, also invoking OpenID Connect identity capabilities as needed. SAML operates primarily in web infrastructure contexts.
Administrative Maintenance
SAML environments demand rigorous coordination during provider changes to update certificates and endpoints across participating sites. OpenID Connect transparently fetches fresh public signing keys as needed at runtime behind the scenes.
Ongoing Federation Management
SAML allows the listing of partner identity providers to scale configuration burden linearly, though with some consistency benefits. OIDC and OAuth require less initial linkage, dynamically federating wider identity universes at the cost of inconsistencies across providers.
Modern Transition Trajectory
While pioneering web SSO, some analysts argue SAML shows signs of aged architectural adversities like key hard-coding and bespoke XML messaging that OAuth and OIDC ecosystem momentum now modernizes with cloud and mobile-first design principles top of mind.
Enhancing Security and User Experience
Beyond architectural comparisons, what matters most is how these protocols impact application security and user experience:
Data Security
OAuth scope specifications combined with OpenID identity claims provide granular yet dynamic control over access to resources that users can understand. SAML relies more on predefined contracts between identity and service providers alone.
Credential Protection
Signed JWT tokens offer tamper proofing with embedded expiration and tenant identifiers for inspection by resource servers across stateless calls. SAML assertions pass similar information but in more bloated XML strings exposed to intermediate replay issues.
Usability
From login UX to multi-device handling, OIDC and OAuth adopt emerging authentication flows and biometrics that users increasingly expect around mobility and portability. The standards continue progressing with human expectations while SAML operates within conventional web constraints.
Visibility and Control
OIDC provides users transparency into data sharing with its consent screen prompts during sign-on. All standards offer some administrative oversight into API integrations and access policies with proper implementation.
Conclusion
This guide just scratches the surface of these pivotal but oft-conflated standards. Their ongoing convergence and divergence for evolving application scenarios warrant continued understanding. Before implementation, carefully evaluate your authentication methods, identity integration needs and access delegation goals to determine the optimal standards combo fitting security imperatives while smoothing adoption.

